# 2014-11-16
What is the IP address of the Windows VM that gets infected?
Answer: 172.16.165.165
What is the host name of the Windows VM that gets infected?
Answer: K34EN6W3N-PC<00>
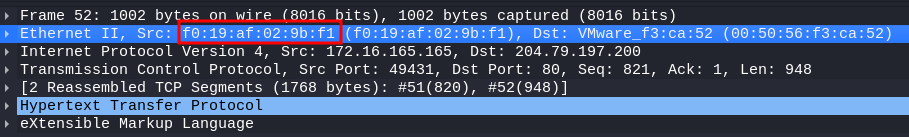
What is the MAC address of the infected VM?
Answer: f0:19:af:02:9b:f1
What is the IP address of the compromised web site?
Answer:
What is the domain name of the compromised web site?
Answer:
What is the IP address and domain name that delivered the exploit kit and malware?
Answer:
What is the domain name that delivered the exploit kit and malware?
Answer:
What is the redirect URL that points to the exploit kit (EK) landing page?
Answer:
Besides the landing page (which contains the CVE-2013-2551 IE exploit), what other exploit(s) sent by the EK?
Answer:
How many times was the payload delivered?
Answer:
Submit the pcap to VirusTotal and find out what snort alerts triggered. What are the EK names are shown in the Suricata alerts?
Answer:
Checking my website, what have I (and others) been calling this exploit kit?
Answer:
What file or page from the compromised website has the malicious script with the URL for the redirect?
Answer:
Extract the exploit file(s). What is(are) the md5 file hash(es)?
Answer: